One of the essential pieces of infrastructure for any company is its IT network. A company’s IT network controls its communication and security information systems. Because of this, securing your company’s IT network and infrastructure is crucial for ensuring efficient business operations. This is done through security infrastructure design, which documents security procedures and carries them out.
By designing a security system for your IT network, you can safeguard your communication systems and data storage against any cybersecurity threats. The importance of infrastructure security means your company should continually update your IT security plans or look into implementing one. In this article, we will look at how these plans can benefit you. Moreover, hiring a technical writer can be the best solution for your cybersecurity needs.
Why Have a Security Infrastructure Design Plan?
First and foremost, as of 2022 companies have increased their investment in the IT network/departments by 40%. Secondly, this heavily relates to a security infrastructure plan, but why has there been such an increase?
The constant development of technology opens up opportunities for your business to innovate and new threats to your IT network. So, whether your business is new or established, large or small, having infrastructure security can benefit you in specific ways. For any business, infrastructure security for its IT network is a necessity. As a new business, securing your IT network offers insurance for your IT network.
By having a security infrastructure design plan in place, you can preemptively anticipate any IT network breach. Established and large businesses with complex IT setups, these companies are a bigger target for cybercriminals. To protect against this, you should continually update your infrastructure security to protect your IT network against new threats.
Once you have implemented an infrastructure security system, you will also see other benefits in addition to your IT network’s protection. With a security infrastructure design plan in place, you can focus more resources on other aspects of your business operations, such as time or funds for business planning and analysis. The increased efficiency of your IT network would also guarantee the speedy and secure delivery of the necessary data for your business decisions. Taking all this into account, security infrastructure design documents improve both the workflow of your business as well as the security.
How to Create a Security Infrastructure Design Plan
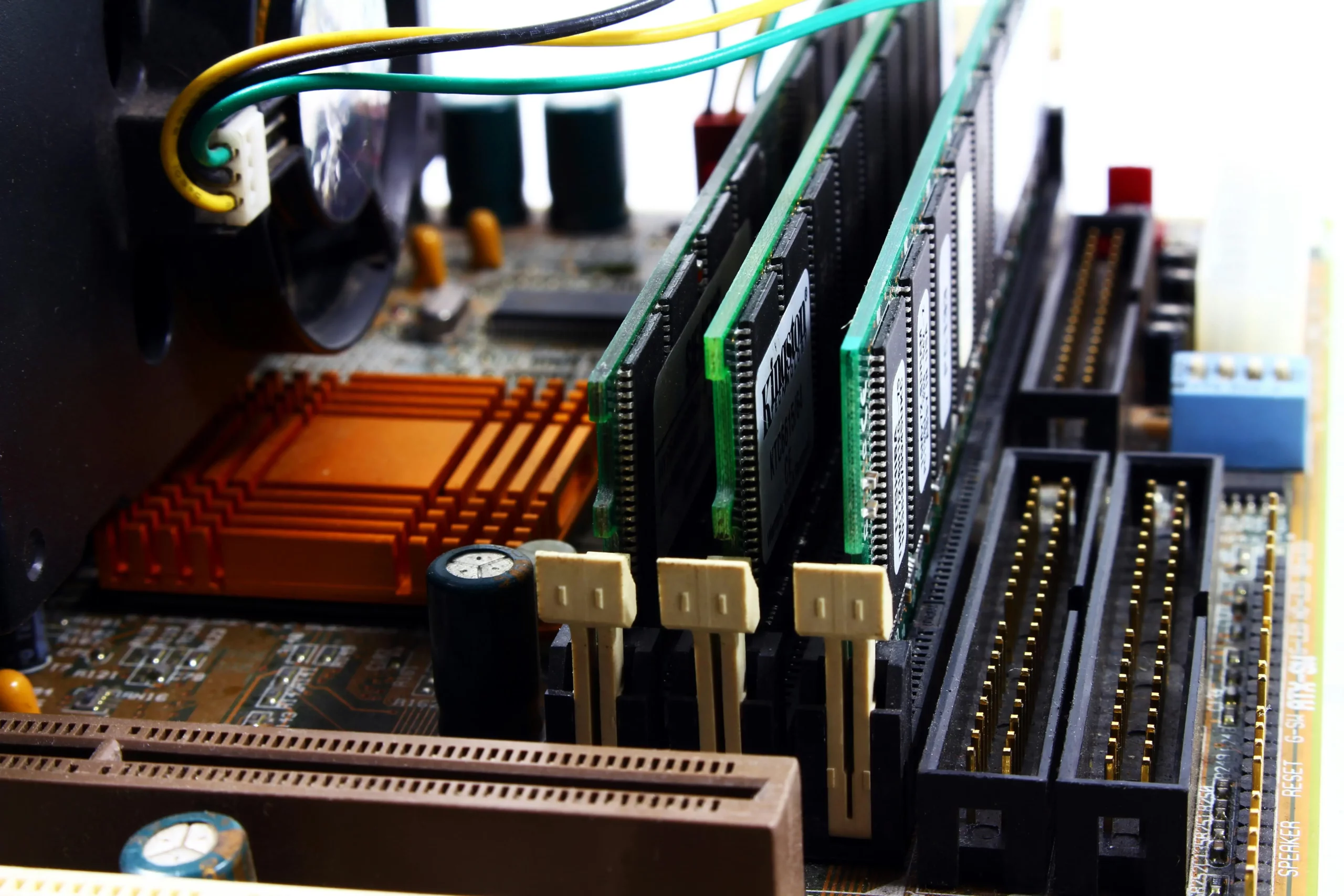
First, a technical writer must gather data for proper security infrastructure design. A well-designed infrastructure security document requires the hardware and software technology used by your company. All the data needed so the writer of the security infrastructure document can create a plan are the risk of each threat, and what different legal and regulatory requirements your company must adhere to.
Every aspect of your IT network must be taken into consideration. From server locations, information flow, connected systems, etc. Combined with the data of your business operations – from your objectives, resource allocation, etc. – your infrastructure security can be designed for the best security possible in accordance with your business needs. This can be what funding there is for security procedures such as encryption software. Another Security gap can be communication flow is more vulnerable than your data storage.
Technical Information Gathering
With all this information gathered, a writer needs to put together a final plan to secure your company’s IT network. Hiring one of EDC’s writers comes with the inherent benefits of a technical writer such as concise writing. Also, EDC’s tech writers have the necessary expertise in cybersecurity, making them a perfect candidate for creating your company’s security infrastructure design documentation. With cybersecurity experience in hand, everything else a technical writer needs for creating a document is the previously mentioned info on your company.
A technical needs to focus on what an infrastructure security design plan needs to accomplish. As previously mentioned, these needs are securing your data, assessing risks, and finally a framework for putting this plan into action. The first step to securing your data is taking a look at what threats are out there. These threats can range from environmental threats (fire in your company’s building), accidental threats (misplacement of important files), and lastly malicious threats (viruses or phishing scams).
Cybersecurity Counter Measures
Once all these threats are identified, a technical writer can come up with countermeasures in order of greatest risk. Potential responses include offsite storage backup for your important data. Other potential responses include securing your servers in a locked room and installing a range of cybersecurity measures for your IT network.
Other counter measures can range in user authentication requirements, encryption of communication, firewalls, securing network access points, and securing data as it travels. These counter measures prevent the risks of losing data, either accidentally or to hackers. These counter measures also provide emergency plans for the loss of servers or potential hardware/software failures.
A technical writer can produce a draft of your security infrastructure design document once all steps are completed. The next steps to take are testing these new security practices. This way you root out further vulnerabilities of your IT network. Lastly, you need to implement the final plan to secure your company’s IT infrastructure.
Conclusion
The importance of technology in businesses is readily apparent with the role of a company’s IT network. From data storage to communication, your IT network facilitates many of the important business processes you need to operate. Because of this, the infrastructure of your IT network should be of the utmost importance.
By hiring one, or a team, of EDC’s technical writers you can guarantee the quality of your security infrastructure design. Cybersecurity for your IT network is a complex subject. The expertise and communication skills of one of EDC’s technical writers allow them to break this subject down into the simplest ways possible. You will easily be able to implement a solution to whatever security documentation needs you have.
How Essential Data Corporation Can Help You
Whether you need a single software technical writer for a brief project or a team of consultants to produce a complete line of documentation, the quality of our work is guaranteed for you. Our clients work closely with an Engagement Manager from one of our 30 local offices for the entire length of your project at no additional cost. Contact us at (800) 221-0093 or sales@edc.us